There is a directed weighted graph that consists of n nodes numbered from 0 to n - 1. The edges of the graph are initially represented by the given array edges where edges[i] = [fromi, toi, edgeCosti] meaning that there is an edge from fromi to toi with the cost edgeCosti.
Implement the Graph class:
Graph(int n, int[][] edges)initializes the object withnnodes and the given edges.addEdge(int[] edge)adds an edge to the list of edges whereedge = [from, to, edgeCost]. It is guaranteed that there is no edge between the two nodes before adding this one.int shortestPath(int node1, int node2)returns the minimum cost of a path fromnode1tonode2. If no path exists, return-1. The cost of a path is the sum of the costs of the edges in the path.
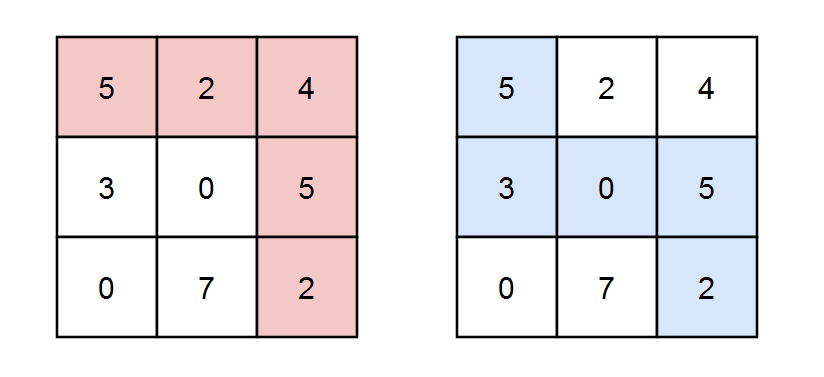
Example 1:
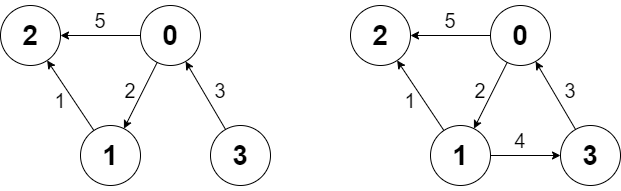
Input ["Graph", "shortestPath", "shortestPath", "addEdge", "shortestPath"] [[4, [[0, 2, 5], [0, 1, 2], [1, 2, 1], [3, 0, 3]]], [3, 2], [0, 3], [[1, 3, 4]], [0, 3]] Output [null, 6, -1, null, 6]
Explanation
Graph g = new Graph(4, [[0, 2, 5], [0, 1, 2], [1, 2, 1], [3, 0, 3]]); g.shortestPath(3, 2); // return 6. The shortest path from 3 to 2 in the first diagram above is 3 -> 0 -> 1 -> 2 with a total cost of 3 + 2 + 1 = 6. g.shortestPath(0, 3); // return -1. There is no path from 0 to 3. g.addEdge([1, 3, 4]); // We add an edge from node 1 to node 3, and we get the second diagram above. g.shortestPath(0, 3); // return 6. The shortest path from 0 to 3 now is 0 -> 1 -> 3 with a total cost of 2 + 4 = 6.
Constraints:
1 <= n <= 1000 <= edges.length <= n * (n - 1)edges[i].length == edge.length == 30 <= fromi, toi, from, to, node1, node2 <= n - 11 <= edgeCosti, edgeCost <= 106- There are no repeated edges and no self-loops in the graph at any point.
- At most
100calls will be made foraddEdge. - At most
100calls will be made forshortestPath.
Solution 1: Floyd-Washall
Time complexity:
Init O(n3)
addEdge O(n2)
shortestPath O(1)
Space complexity: O(1)
C++
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 |
// Author: Huahua class Graph { public: Graph(int n, vector<vector<int>>& edges): n_(n), d_(n, vector<long>(n, 1e18)) { for (int i = 0; i < n; ++i) d_[i][i] = 0; for (const vector<int>& e : edges) d_[e[0]][e[1]] = e[2]; for (int k = 0; k < n; ++k) for (int i = 0; i < n; ++i) for (int j = 0; j < n; ++j) d_[i][j] = min(d_[i][j], d_[i][k] + d_[k][j]); } void addEdge(vector<int> edge) { for (int i = 0; i < n_; ++i) for (int j = 0; j < n_; ++j) d_[i][j] = min(d_[i][j], d_[i][edge[0]] + edge[2] + d_[edge[1]][j]); } int shortestPath(int node1, int node2) { return d_[node1][node2] >= 1e18 ? -1 : d_[node1][node2]; } private: int n_; vector<vector<long>> d_; }; |
Solution 2: Dijkstra
Time complexity:
Init: O(|E|) ~ O(n2)
AddEdge: O(1)
ShortestPath: O(|V|*log(|E|)) ~ O(n*logn)
Space complexity: O(E|) ~ O(n2)
C++
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 |
// Author: Huahua class Graph { public: Graph(int n, vector<vector<int>>& edges): n_(n), g_(n) { for (const auto& e : edges) g_[e[0]].emplace_back(e[1], e[2]); } void addEdge(vector<int> edge) { g_[edge[0]].emplace_back(edge[1], edge[2]); } int shortestPath(int node1, int node2) { vector<int> dist(n_, INT_MAX); dist[node1] = 0; priority_queue<pair<int, int>, vector<pair<int, int>>, greater<>> q; q.emplace(0, node1); while (!q.empty()) { const auto [d, u] = q.top(); q.pop(); if (u == node2) return d; for (const auto& [v, c] : g_[u]) if (dist[u] + c < dist[v]) { dist[v] = dist[u] + c; q.emplace(dist[v], v); } } return -1; } private: int n_; vector<vector<pair<int, int>>> g_; }; |